376 posts
- Tips and Best Practices
- Threat Prevention
- Social Media
- Our Products
- News and latest trends
- IOT
- Digital Education
- Artificial Intelligence
Tips and Best Practices
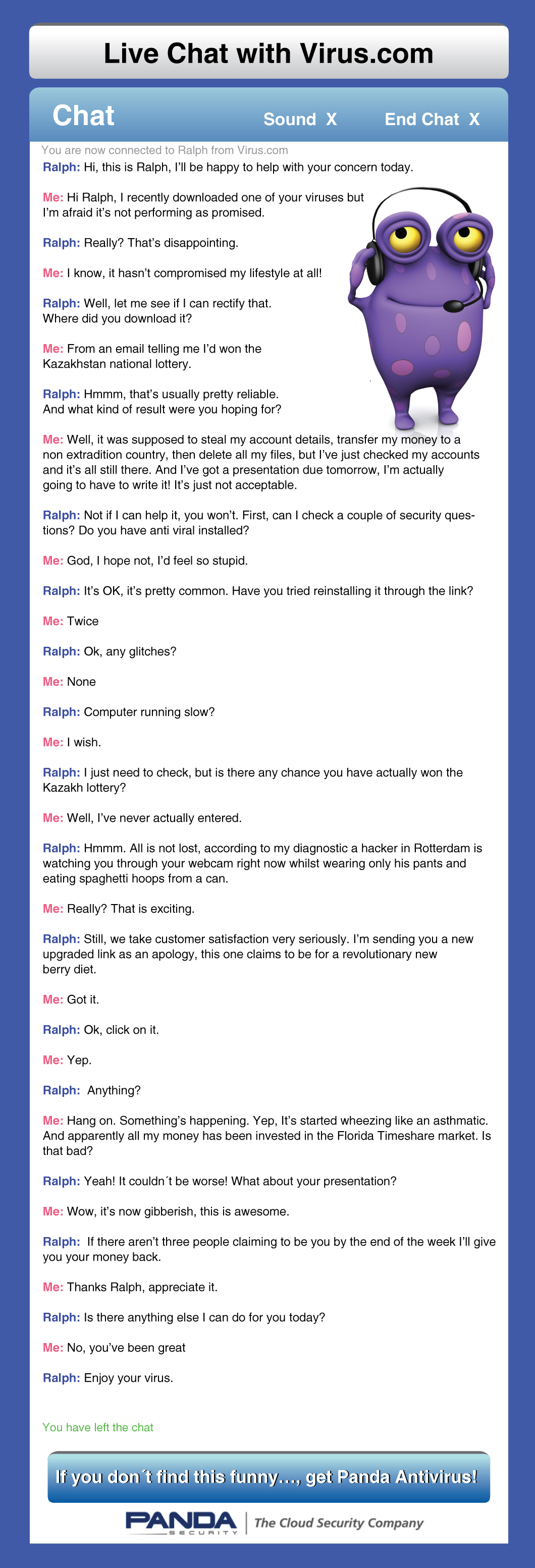
419 scam. How to recognize it
If you have an email address no doubt at some time or another you have received an email from some friendly soul claiming that you’ve…
4 steps to avoid viruses
Protecting your computer is much easier than you might think. Follow these 4 steps and your computer won’t become infected again!
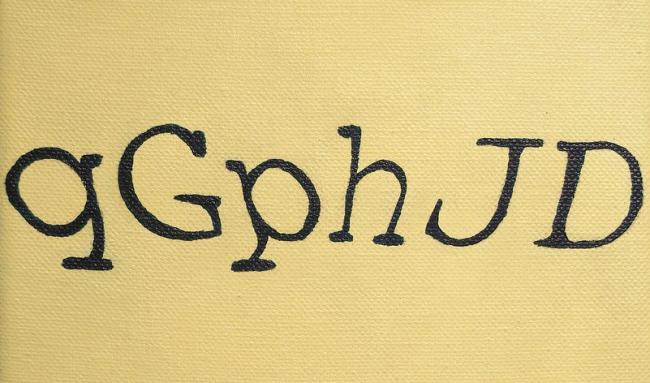
Fed up with CAPTCHA? How to avoid it?
It is always annoying. You enter a website and suddenly, a CAPTCHA assaults you in doubt over whether you are human or a robot…
Keep your private details safe from viruses
If you want to share this inphographic, here you have the code:
What to look for in business antivirus?
One anti-malware solution is not the same as another, and there are many factors to consider when choosing one. Firstly, you need to know your…
6 tips for those who want to work at Panda Security
People often ask us what you have to do or what you need to be able to work in Panda Security. So today we’re…
Tips for protecting children on the Internet
Have your kids got a tablet? Or their own computers? A phone with Internet access? The answer is probably ‘yes’. There was a time…