422 posts
- Tips and Best Practices
- Threat Prevention
- Social Media
- Our Products
- News and latest trends
- IOT
- Digital Education
- Artificial Intelligence
Threat Prevention
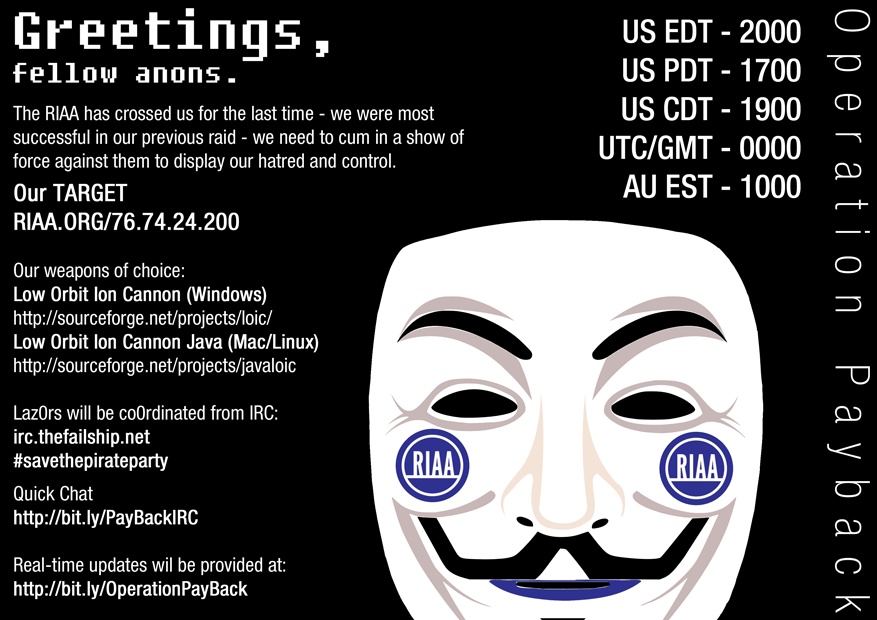
PandaLabs Publishes Exclusive Interview with Masterminds Behind Anti-Piracy Cyber Protest “Operation Payback”
Q&A with leaders of “Anonymous” group responsible for the attacks on the Motion Picture Association of America and others available on the PandaLabs blog PandaLabs,…
PandaLabs Quarterly Report (July-September 2010)
We have just published the latest PandaLabs Quarterly Report, which covers the main topics related to computer security that have happened between July and September…
The Brazilian Army and Panda Security join forces to combat cyber-warfare
– This agreement will see Panda support the Brazilian Army in the professionalization of its operational agents in the fight against cyber terrorism, digital crime…
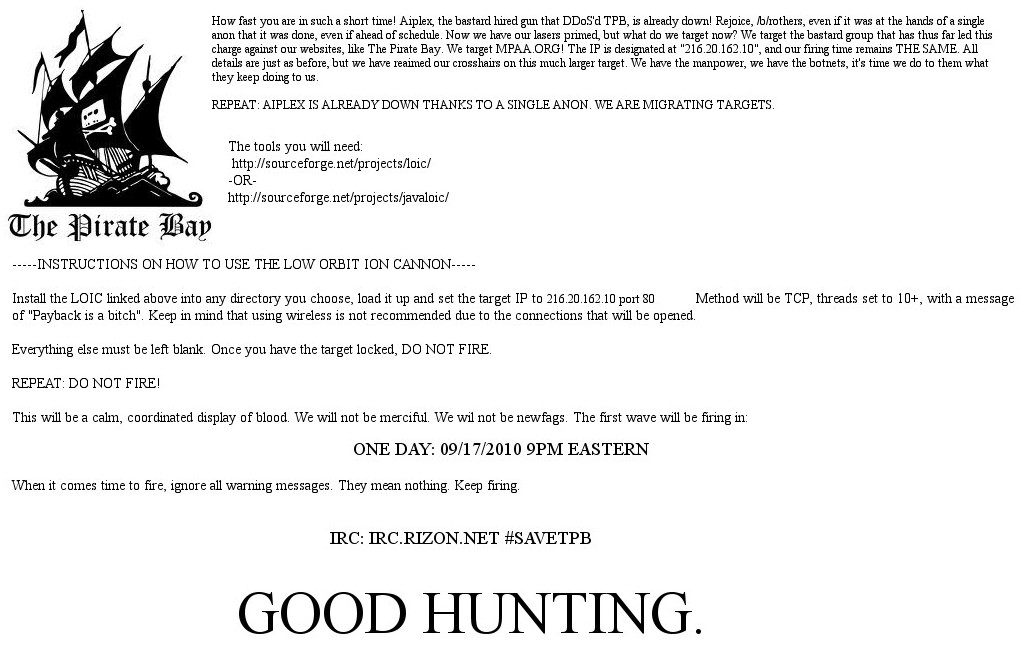
Mass cyber-protests across the Web target Recording Industry Association of America and Motion Picture Association of America
In response to the attempt to shut down free file-sharing sites, such as The Pirate Bay, 4chan users have organized to launch denial of service…
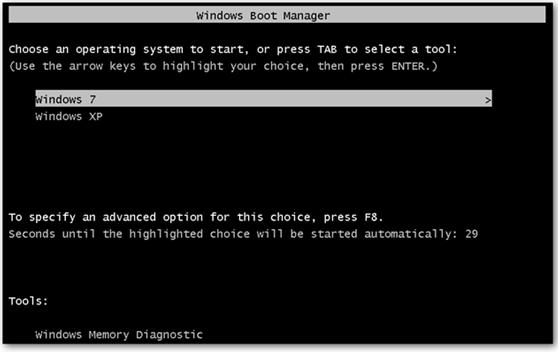
Dual boot: an unexpected ally
Posted by Javier Guerrero, 15th September 2010 At Panda Security we are relentless in our efforts to advise users about the best way of protecting…
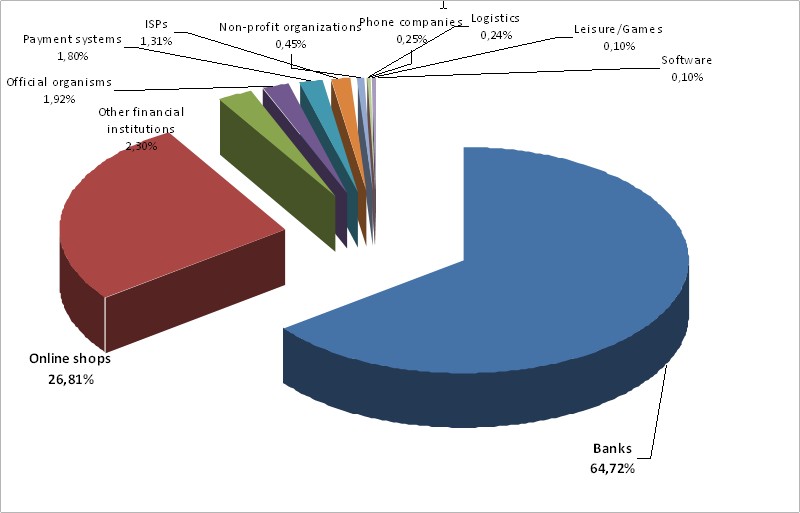
Every week, hackers are creating 57,000 new fake Web addresses to trick or infect users
In an average week, hackers use some 375 different high-profile names and company brands to lure users: 65% of fake websites imitate bank pages, followed…
Rootkits – The Invisible Threat
Malware is no longer viewed with the notoriety it once was. Gone are the days of massive infections, such as the “I love you” worm,…