Search Results for
POS
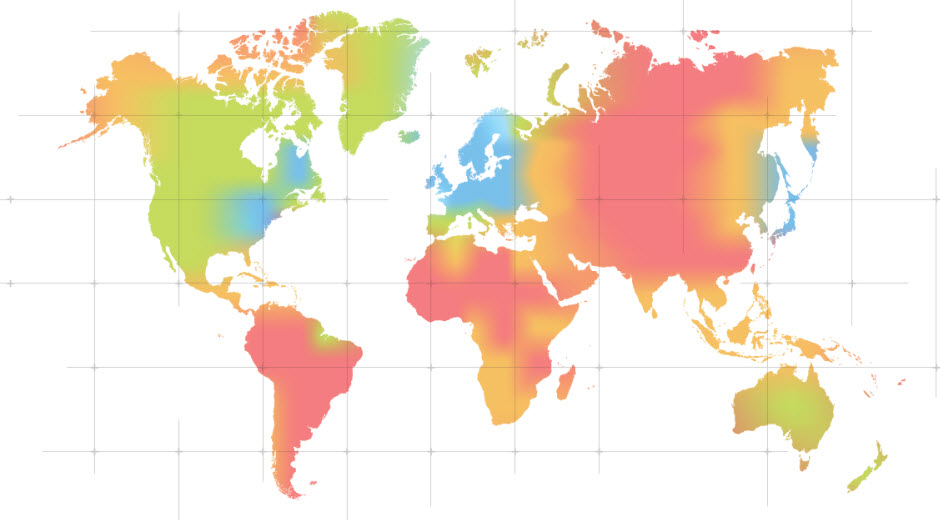
Security forecast for 2015
Our colleagues at PandaLabs have been making their predictions about what will be happening in the world of IT security in 2015. Do you want…
Can they spy on you through your smartphone microphone?
Smartphone users are highly sensitive about privacy, not least because so much personal data is stored in just a few square centimeters. We shudder at…
Major security attacks in 2014 – Part 2
A few days ago we published a summary of six of the most important security attacks in 2014. Today we continue this list with some…
Prevention is better than cure: These eleven threats could compromise your corporate systems in 2015
We don’t know what next year has in store for us, yet predictions are always useful to be better prepared for what might be around…
Christmas contest! – Help us to get a safe Christmas!
As you have no doubt seen, these days we have been posting a series of articles to help ensure everyone enjoys a safe and happy…
5 tips to avoid a ‘nightmare before Christmas’
If you’re going away, don’t post details on social networks about where you are or when you’re returning. It’s better not to share this kind…
The Snowden effect: Has cyber-espionage changed the way we view security?
In the history of international espionage in general and specifically in the case of the US National Security Agency (NSA), there has been a turning…