Search Results for
BEC
BlogdeBori: A community manager working with Web 2.0 tools
I’ve never been particularly good at describing myself, in fact I find descriptions unnecessary in most cases. At school this was the thing I most…
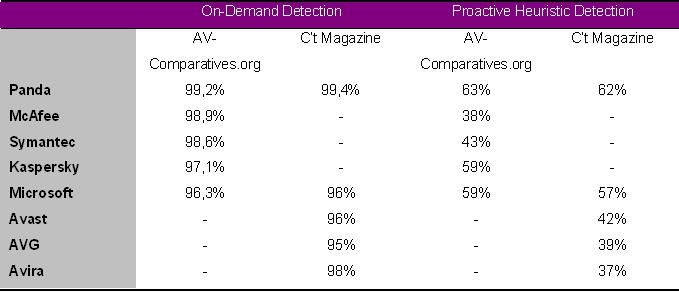
Panda Security Consistently Receives Top Scores in Most Recent Independent Anti-Malware Comparative Tests
Company’s cloud protection model also gets top honors in recent independent reviews from CNET, PCMag.com and About.com Panda Security today announced results from several independent…
Decoding the United States Cyber Command Seal
If you’re a frequent reader of the PandaLabs blog, then you know that we love creating crypto/crackme challenges. In fact, we have one coming up…
PandaLabs advises caution with travel planning and geolocation applications
In addition to security problems associated with unsecure WiFi networks, cyber-cafes, etc, applications that indicate the user’s location and information exchanged across social networks also…
Viruses designed for iPhones can also infect iPads
– PandaLabs demonstrates in this video how malware designed for cell phones can also affect the popular iPad. – The iPhone/Eeki worm appeared last year, infecting jailbroken…
Infecting the iPad }:-)
Last year we witnessed the first infection that affected devices based on the iPhone operating system, it was the worm iPhone/Eeki. We wrote a blog…
What is the ‘Cloud’ and what is Collective Intelligence?
What is the ‘cloud’? Cloud computing is a technology that allows services to be offered across the Internet. To this effect, the term ‘the cloud’…