Search Results for
BEC
Teaching cyber-security from school age
As the Internet increasingly becomes part of our everyday lives and we use new technologies in all areas of our life, there’s an ever greater…
Spanish hacker manages to control every room at a luxury hotel remotely
Imagine the following situation. You arrive at your hotel. And not just any hotel, no. A gorgeous 5-star hotel that occupies the top 28 floors…
Recycled code may compromise the security of Android apps
Android is essentially an open-source operating system where anyone can contribute (manufacturers can integrate it freely in their own devices), and the community of Android…
Cyber-criminals increasingly use bots disguised as Google Web spiders to infiltrate websites.
When you enter any word in Google’s search engine, even though the result might not be spot on at the first go, there is a…
The USA aims to turn veterans into cyber-warriors
Paradoxically, there is a hole in cyber-security, at least when it comes to personnel. Even though businesses and institutions are increasingly aware of the importance…
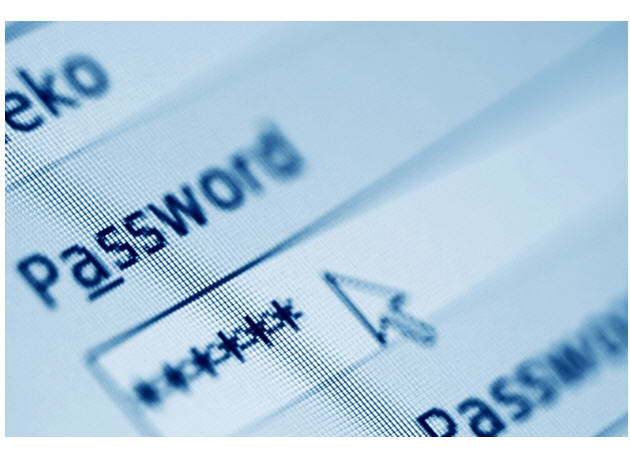
The largest ever theft of passwords uncovered
What appears to be the greatest theft of user credentials in history has been reported by Hold Security, a small US security firm. No less…
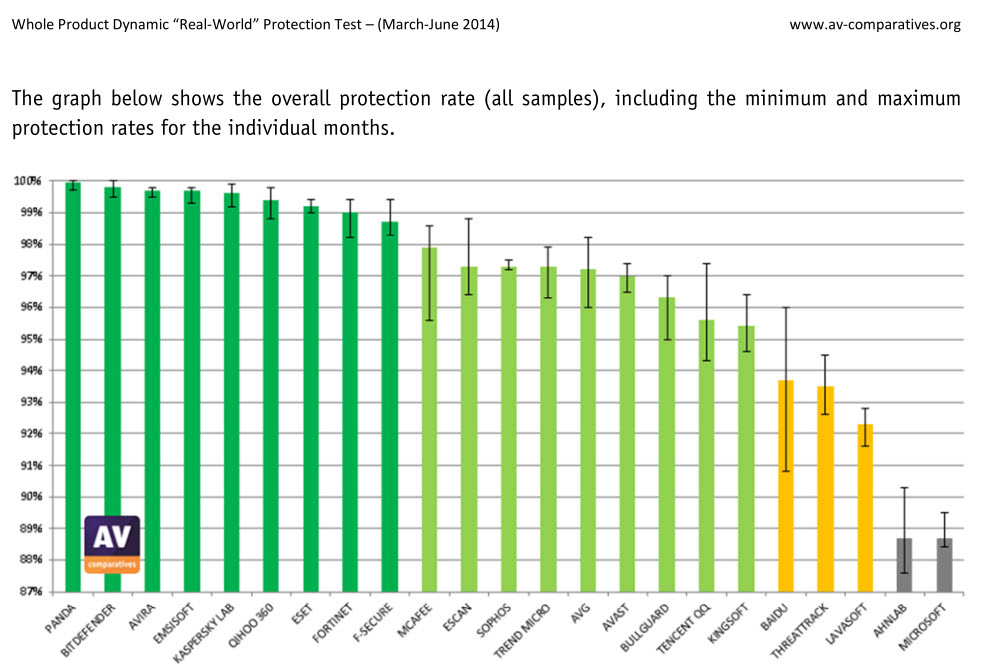
Panda Security, Number 1 in protection according to AV.Comparatives
We couldn’t be happier! Why? Because of the results of the latest AV.Comparatives test! Panda Security has been declared number one by AV.Comparatives, in…