Search Results for
BEC
10 tips for protecting your privacy when everything seems against it
We are always talking about the dangers that our data often faces in the Internet. Constant leaks and vulnerabilities in the services we use the…
When cyber-attacks cause physical damage
We are used to hearing about cyber-attacks and the massive damage they cause to those affected. You do not need to go too far back…
‘The Imitation Game’: The greatest milestone in the history of cryptography hits the big screen
A war hero in a mathematician’s skin. That was Alan Turing. The man considered the father of computer science played a key role during World…
The most cyber-attacked city is a model town
There’s a city in a secret place in the state of New Jersey where the public services are always a mess. Power cuts, water supply…
WhatsApp blocks WhatsApp Plus users
“You’re temporarily banned from WhatsApp because you may have violated our terms of service. You’ll be able to use WhatsApp again in:” Maybe this text…
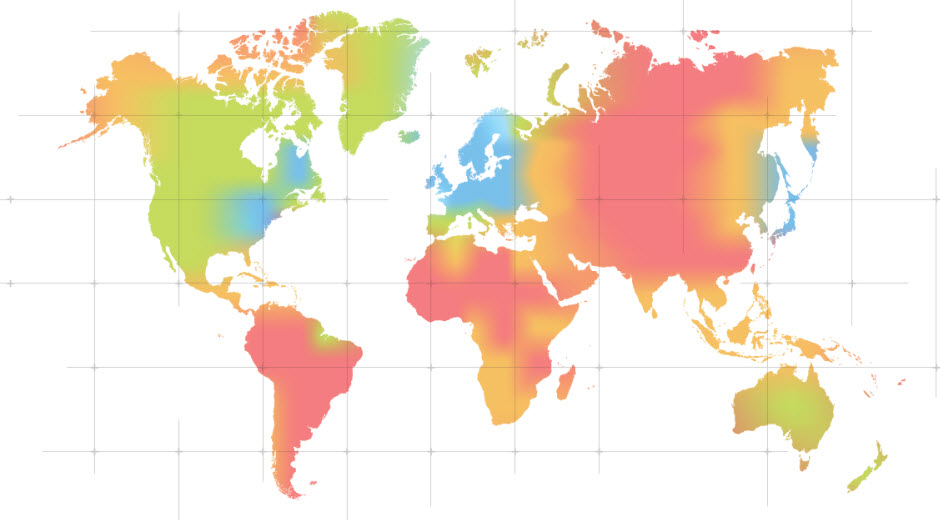
Security forecast for 2015
Our colleagues at PandaLabs have been making their predictions about what will be happening in the world of IT security in 2015. Do you want…
Can they spy on you through your smartphone microphone?
Smartphone users are highly sensitive about privacy, not least because so much personal data is stored in just a few square centimeters. We shudder at…