Search Results for
BEC
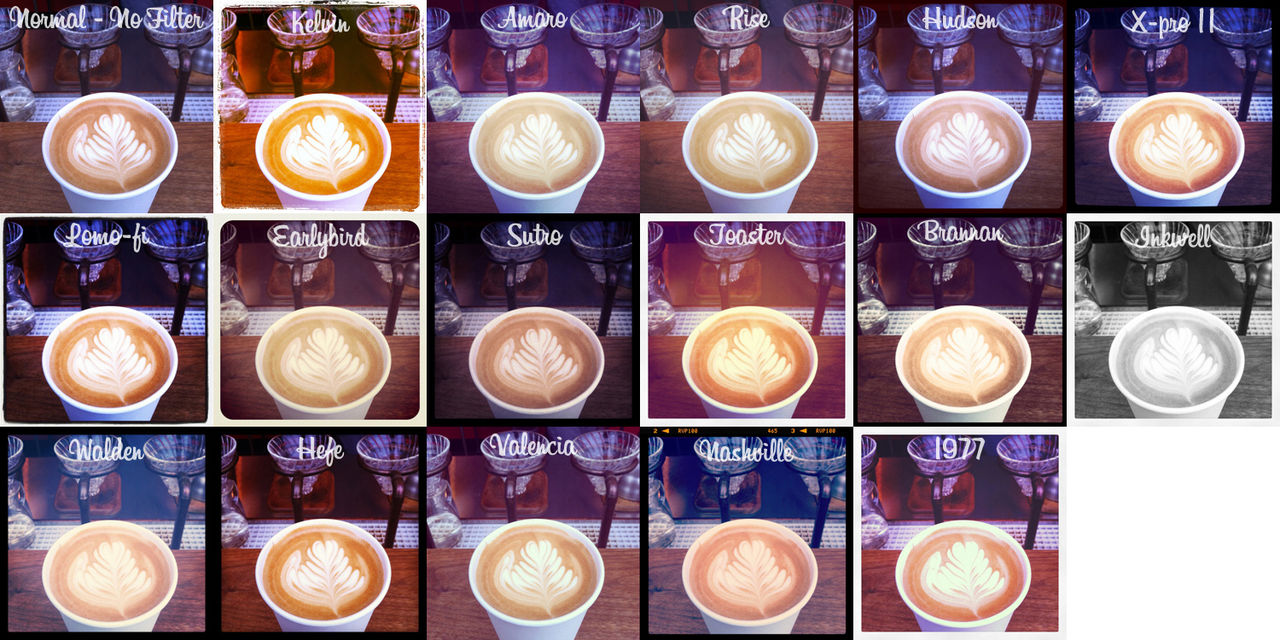
Celebrities on Instagram. Are they putting their lives at risk?
Celebrities around the World, beware! Many of us have surrender to Instagram, but we have to advice that we are endangering ourselves! One can easily…
Panda Security: 25 years fighting against malware
Already 25 years together? It seems like yesterday when a group of friends in Bilbao started this adventure! Who would have thought that, 25 years…
Cyber-criminals set their sights on drones
More and more cameras are watching us from the sky. And no, they don’t belong to the police or some intelligence agency, but to your…
What are Advanced Persistent Threats? Interview with Fernando Andrés
On several occasions we have discusses the need for effective protection against Advanced Persistent Threats in corporate environments, however, do companies really know what we…
How to secure the files your company stores in the cloud
Goodbye CD, DVD and pen drive. When you need to share a document with a work colleague or you have to take work home, you…
Dating Apps on your company’s phone. Be careful not to reveal too much personal information!
Your personal life is not incompatible with your professional life, and even less so on your smartphone, a device we use for almost everything these…
The vulnerable Internet of Things: Security when everything is connected
The Internet of Things is here to stay. Soon, all of our home appliances will be virtually linked. Televisions, clocks, alarms, cars and even fridges…